
Using AI to Detect and Prevent Ransomware in Government Systems
At 11:47 PM on a Tuesday in February 2024, a ransomware strain called Akira quietly began encrypting files across Fulton County, Georgia’s government network. Within hours, court systems were offline, property records were inaccessible, and emergency communications were strained. The attack cost millions and exposed a truth that every public sector IT leader already knows but rarely has the budget to address: government systems are high-value, chronically under-defended targets.
This isn’t a fringe problem. According to Emsisoft’s 2024 State of Ransomware report, over 160 government entities in the United States were hit by ransomware in a single year. The average recovery cost for a public sector organization now exceeds $2.8 million and that’s before you factor in reputational damage and community disruption.
The uncomfortable reality? Traditional signature-based antivirus and perimeter firewalls were never designed for today’s threat landscape. But a new generation of AI ransomware detection tools is changing the game and governments that act now will be the ones still standing when the next attack happens.
Key Challenges: Why Government Is a Prime Target
Before we talk solutions, we need to understand why defending public sector networks is uniquely difficult:
- Legacy Infrastructure at Scale: Many county and state agencies run Windows 7-era systems that can’t be patched without breaking mission-critical applications. These aren’t negligent oversights they’re operational realities baked in by procurement cycles and limited budgets.
- Flat, Over-Connected Networks: A ransomware attack today on government networks spreads so rapidly precisely because departments often share flat network segments. A compromised HR workstation can reach court case management files in minutes.
- Understaffed IT Teams: A county with 800 employees might have three IT staff members. They’re responsible for helpdesk tickets and cybersecurity strategy simultaneously.
- Data Richness Makes Government Irresistible: Social security numbers, court records, tax data, voter rolls the combination of sensitive personal data and operational criticality makes public sector systems among the most lucrative ransomware targets on the planet. Public sector cyberattacks have tripled since 2019.
- Compliance Without Teeth: FISMA, NIST 800-53, and CJIS frameworks provide guidance, but compliance ≠ security. Many agencies check the box without implementing the behavioral controls that actually stop attacks.
Emerging Tech Trends Solving the Problem
The cybersecurity industry’s response to this crisis has been dramatic. Here’s what’s actually moving the needle in 2026:
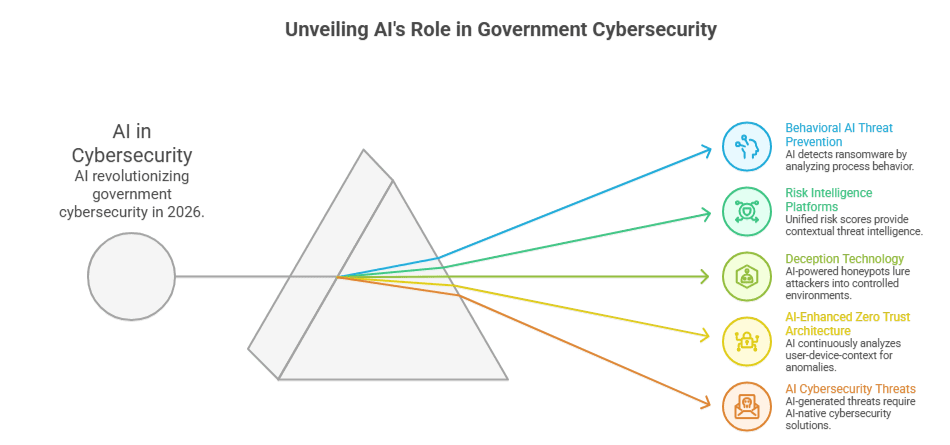
1. Behavioral AI Threat Prevention (Not Just Signatures)
Modern AI threat prevention platforms don’t ask “does this file match a known malware signature?” They ask: “is this process behaving like ransomware?” AI models trained on billions of endpoint events can detect encryption-like file system activity, lateral movement patterns, and credential harvesting in real time catching zero-day variants before they hit any threat database.
2. Risk Intelligence Platforms
A risk intelligence platform aggregates threat data across endpoints, network traffic, email, and identity systems into a unified risk score. Instead of siloed alerts that overwhelm analysts, these platforms surface prioritized, contextual intelligence telling your team not just that something happened, but what it means and what to do next.
3. Deception Technology
AI-powered honeypots and deception grids are being deployed in government networks to lure attackers into controlled environments. When ransomware actors “find” a fake file server full of convincing decoy data, they reveal their presence, TTPs (tactics, techniques, and procedures), and lateral movement paths all while touching nothing real.
4. Zero Trust Architecture (AI-Enhanced)
Zero Trust isn’t new, but AI-enhanced ZTA is. Instead of static access rules, machine learning models continuously analyze whether a given user-device-context combination is behaving normally. An administrator logging in from their usual workstation at 9 AM looks very different from the same credentials used at 2 AM from a new device and AI flags the difference instantly.
5. AI Cybersecurity Threats Are Also Evolving
It would be incomplete not to mention the flip side: AI cybersecurity threats in 2026 are expected to include AI-generated phishing campaigns that bypass traditional email security, AI-assisted vulnerability discovery, and polymorphic ransomware that rewrites itself to evade behavioral detection. The arms race is real which is exactly why government agencies need AI-native defenses, not bolt-on tools.
Step-by-Step: How to Implement AI-Powered Ransomware Defense
Here’s a practical roadmap for government IT leaders ready to act:
Step 1 — Baseline Your Current Exposure Before you can defend, you need to see. Deploy an asset discovery tool to map every endpoint, server, and network device including forgotten IoT devices and printers. You cannot protect what you don’t know exists.
Step 2 — Implement Endpoint Detection & Response (EDR) with AI Replace legacy antivirus with a modern EDR solution powered by machine learning. Platforms like CrowdStrike Falcon, Microsoft Defender for Endpoint, or SentinelOne provide real-time behavioral AI for cyber defense at the endpoint level, with autonomous containment capabilities that can isolate a compromised machine in milliseconds.
Step 3 — Deploy a Risk Intelligence Platform Centralize your visibility. A government IT solutions stack without a centralized SIEM or XDR platform is like having security cameras with no monitor. Platforms purpose-built for federal government IT solutions such as Splunk Government Cloud or Palo Alto Cortex XDR can ingest and correlate signals at scale.
Step 4 — Segment Your Network Aggressively Micro-segmentation is your best brake pedal against ransomware spread. Separate HR from Finance from Public Safety from Court Systems. Use software-defined networking where possible to make these boundaries enforceable in software, not just policy documents.
Step 5 — Harden Identity with MFA and Privileged Access Management Over 70% of ransomware attacks leverage stolen credentials. Enforce multi-factor authentication universally including on VPN, RDP, and administrative consoles. Layer in PAM (Privileged Access Management) to ensure that even if a regular account is compromised, it can’t reach your most critical systems.
Step 6 — Build and Test an Incident Response Plan An untested IR plan is essentially no plan. Conduct tabletop exercises that simulate a ransomware attack today on government infrastructure. Know who calls who, when to notify law enforcement (FBI Cyber Division, CISA), and what your backup restoration timeline actually looks like under pressure.
Step 7 — Train Staff Continuously, Not Annually Phishing simulations, micro-learning modules, and real-time coaching tools transform your workforce from the largest vulnerability into a genuine detection layer. Humans catch what machines miss and vice versa.
Real-World Use Cases
Dallas, Texas (2023): A ransomware attack by Royal disrupted court systems and 911 dispatch. The city’s recovery took weeks. Post-incident, Dallas invested in a full XDR deployment and network micro-segmentation a playbook now being adopted by peer cities across Texas.
Colorado Department of Transportation (2018 → Lessons Applied): After a SamSam ransomware attack cost $1.5 million to remediate, CDOT rebuilt its security architecture around zero-trust principles and AI-driven anomaly detection, becoming one of the early government case studies for what AI-enhanced government data security looks like in practice.
New York City Health + Hospitals: Facing constant threat exposure as a healthcare-adjacent public entity, NYC H+H deployed behavioral AI and deception technology across its network, reducing mean-time-to-detect (MTTD) for suspicious activity from 72 hours to under 4 hours.
These examples reinforce a simple truth: defending your community against cyber threats requires investment in modern tooling, not just more compliance paperwork.
Best Practices & Expert Tips
Drawing on frameworks from CISA, NIST, and cybersecurity practitioners embedded in state and local government:
Align your security investments to the NIST Cybersecurity Framework 2.0 “Govern” function leadership accountability matters as much as technology. Establish a security steering committee that includes elected officials or department heads, not just IT.
Leverage CISA’s free services aggressively: the Cyber Hygiene (CyHy) vulnerability scanning program, the Ransomware Readiness Assessment (RRA), and the Multi-State ISAC (MS-ISAC) provide world-class resources specifically designed for cybersecurity solutions for government entities of all sizes.
Prioritize immutable, offline backups. AI detection is your first line of defense; verified backups are your last. Test restores quarterly. Know your RTO and RPO before you need them.
Treat supply chain vendors as attack surfaces. The SolarWinds breach proved that even trusted software vendors can become ransomware delivery mechanisms. Vet your vendors security postures, require SOC 2 reports, and limit vendor access to only the systems they need.
Common Mistakes to Avoid
Investing in tools without investing in people is the most common failure pattern. AI and automation reduce analyst workload they don’t eliminate the need for skilled security professionals who understand your specific environment.
Treating ransomware defense as an IT problem rather than an organizational risk is equally dangerous. When leadership doesn’t understand the stakes, budgets don’t materialize and accountability disappears.
Neglecting lateral movement prevention while focusing only on entry-point security is like installing a strong front door while leaving interior doors unlocked. Perimeter defense alone is insufficient in 2026.
Finally, never underestimate the human element in incident response. When a ransomware attack hits, panic is the enemy of good decision-making. Pre-established communication trees, legal contacts, and public communications templates save critical time.
Conclusion: The Future of AI-Powered Government Cyber Defense
The trajectory is clear. By 2026 and beyond, AI cybersecurity threats will be more sophisticated, more automated, and more targeted than anything we’ve seen. Ransomware groups are already using AI to identify vulnerable government systems, craft convincing spear-phishing emails, and optimize encryption routines.
But the defenders are also leveling up.
The next frontier includes autonomous AI security operations centers capable of detecting, investigating, and containing threats with minimal human intervention critical for resource-constrained government agencies. Federated machine learning models will allow agencies to share threat intelligence without exposing sensitive network data. And advances in quantum-resistant cryptography will begin replacing vulnerable encryption protocols across federal infrastructure.
The agencies that win this fight won’t be the ones that spent the most money. They’ll be the ones that built layered, AI-native defenses, invested in their people, and treated cybersecurity as a leadership priority rather than an IT afterthought.
How Government App Maisters Can Help
Government App Maisters specializes in delivering enterprise-grade cybersecurity solutions for government at the state, local, and federal level. From deploying Risk Intelligence Platforms to designing zero-trust architectures tailored to public sector constraints, our team brings deep domain expertise to agencies of every size.
We understand that government IT doesn’t operate like the private sector procurement timelines, compliance requirements, legacy system dependencies, and public accountability all shape what “good security” looks like in practice. Our solutions are designed with those realities in mind.
Whether you’re beginning your AI ransomware detection journey or hardening an existing security stack against the next generation of threats, Government App Maisters is your trusted partner in defending your community against cyber threats.
Ready to assess your ransomware readiness? Contact Government App Maisters today.
Frequently Asked Questions
Why are government agencies frequently targeted by ransomware attacks?
Government agencies hold high-value data Social Security numbers, court records, tax information, and voter rolls while often running outdated infrastructure with understaffed IT teams. This combination of sensitive data and weaker defenses makes public sector networks among the most attractive targets for ransomware groups.
How does AI detect and prevent ransomware in government systems?
AI detects ransomware by monitoring behavioral patterns in real time flagging unusual file encryption activity, lateral movement, and credential misuse before significant damage occurs. Unlike traditional antivirus, it doesn’t rely on known threat signatures, so it can stop zero-day ransomware variants that have never been seen before.
What is a Risk Intelligence Platform and how does it help government cybersecurity?
A Risk Intelligence Platform aggregates threat data from endpoints, networks, email, and identity systems into a single dashboard with prioritized risk scores. It replaces overwhelming alert volumes with actionable intelligence, helping small government IT teams focus on the threats that matter most.
What cybersecurity steps should government agencies take to prevent ransomware?
Government agencies should deploy AI-powered endpoint detection and response (EDR), enforce multi-factor authentication, segment their networks, and maintain verified offline backups. CISA also offers free tools including vulnerability scanning and Ransomware Readiness Assessments purpose-built for public sector organizations.
What should a government agency do immediately after a ransomware attack?
Immediately isolate affected systems from the network to stop the spread, then contact the FBI Cyber Division and CISA for incident support. Activate your incident response plan, assess backup integrity, and avoid paying the ransom documented recovery through backups is always the preferred path.
Can small government agencies with limited budgets defend against ransomware?
Yes. Small agencies can start with free CISA resources like the Multi-State ISAC (MS-ISAC) and Cyber Hygiene scanning program. Prioritizing multi-factor authentication, immutable backups, and basic network segmentation delivers meaningful protection before investing in advanced AI security tools.
How are AI cybersecurity threats expected to evolve by 2026?
By 2026, ransomware groups are expected to use AI to craft highly targeted phishing campaigns, automate vulnerability discovery, and deploy polymorphic malware that rewrites itself to evade detection. This makes AI-native defense not traditional security tools the only viable long-term strategy for government networks.
How can Government App Maisters help protect our agency from ransomware?
Government App Maisters delivers purpose-built cybersecurity solutions for government agencies including AI ransomware detection, Risk Intelligence Platform deployment, and zero trust architecture design. Their team specializes in the unique compliance and legacy infrastructure realities of public sector IT, helping agencies of all sizes build lasting cyber resilience.






