How Government Portals Are Fighting Ransomware Threats
On a Tuesday morning in 2023, Dallas, Texas woke up to a city in digital crisis. The Royal ransomware group had infiltrated municipal systems, shutting down courts, utilities, and 911 dispatch services for days. It wasn’t an isolated incident it was a warning shot heard across every statehouse, county courthouse, and federal agency in the country.
A ransomware attack today on government infrastructure isn’t a hypothetical threat buried in a risk report. It’s a Tuesday morning. It’s a hospital diverting ambulances. It’s a school district unable to process payroll. It is, increasingly, the front line of modern warfare and most government portals were built for a different era.
According to Statista, ransomware attacks on the public sector surged by over 70% between 2022 and 2024. The average ransom demand against government entities now exceeds $2.5 million, and that figure doesn’t include recovery costs, litigation, and the irreversible erosion of public trust. The stakes have never been higher.
So how are government cybersecurity defense teams fighting back and winning?
Key Challenges: Why Government Portals Are Uniquely Vulnerable
Government agencies face a paradox that private enterprises don’t. They must remain radically open accessible to every citizen, 24/7, across every device while simultaneously guarding some of the most sensitive data on earth: tax records, criminal histories, social security information, health data, and national security intelligence.
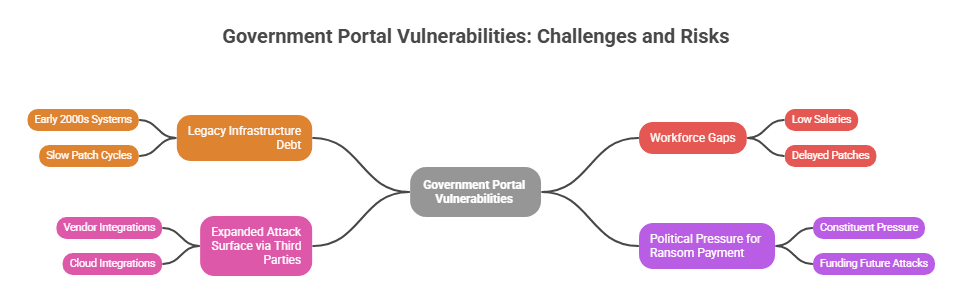
The core vulnerabilities include:
- Legacy Infrastructure Debt: Many state and federal portals still run on systems architected in the early 2000s. Patch cycles are slow, budgets are constrained, and the attack surface grows wider every year as new services move online.
- Workforce Gaps: The public sector competes poorly with private tech salaries for cybersecurity talent. Understaffed IT teams mean delayed patches, unmonitored endpoints, and alert fatigue that lets real threats slip through.
- Expanded Attack Surface via Third Parties: Modern government IT solutions rely on a web of vendors, contractors, and cloud integrations. Each integration is a potential entry point. The SolarWinds attack which compromised dozens of federal agencies exploited exactly this trust.
- Political Pressure for Ransom Payment: Unlike corporations, government officials face constituent pressure to restore services fast. This urgency can push decision-makers toward payment, which funds future attacks and signals that government targets pay.
Public sector cyberattacks increasingly target the supply chain and citizen-facing portals because these are simultaneously the most visible and often the least hardened.
Emerging Tech Trends Reshaping Government Cyber Defense
The good news: a generation of technologies is reshaping what ransomware protection strategies look like in 2025 and beyond.
1. AI-Driven Threat Detection: Modern ai cybersecurity threats 2026 analysis relies on machine learning models that detect behavioral anomalies unusual file encryption patterns, lateral movement across networks, or privilege escalation in milliseconds. Tools like Darktrace, CrowdStrike Falcon, and Microsoft Defender for Government now offer AI models trained specifically on public sector attack patterns.
2. Zero Trust Architecture (ZTA): The old “castle and moat” model of perimeter defense is dead. Zero Trust assumes breach and verifies every user, every device, every request continuously. CISA’s Zero Trust Maturity Model has become the de facto roadmap for federal government IT solutions, pushing agencies toward identity-centric security.
3. Risk Intelligence Platforms: A Risk Intelligence Platform aggregates threat feeds, dark web monitoring, vulnerability data, and behavioral analytics into a unified dashboard. Platforms like Recorded Future and Threat Connect give government security teams predictive insight not just reactive alerts enabling them to act before ransomware groups pull the trigger.
4. Immutable Cloud Backups: Cloud-native backup solutions with write-once, read-many (WORM) storage mean that even if ransomware encrypts a primary environment, agencies can restore to a clean state within hours. This fundamentally breaks the ransomware business model.
5. Automated Incident Response (SOAR): Security Orchestration, Automation and Response platforms can isolate an infected endpoint, revoke compromised credentials, and notify leadership all within seconds of detection, without human intervention.
Step-by-Step Solutions: Building a Ransomware-Resilient Government Portal
Step 1: Conduct a Threat Exposure Assessment Before deploying any tool, understand your attack surface. Map every public-facing endpoint, every third-party integration, and every legacy system. Prioritize based on data sensitivity and service criticality. Use your risk intelligence platform to benchmark exposure against peer agencies.
Step 2: Implement Multi-Factor Authentication (MFA) Everywhere Over 80% of ransomware attacks begin with compromised credentials. Mandate phishing-resistant MFA (FIDO2/hardware keys) for all privileged accounts and remote access points. This single step eliminates the most common initial access vector.
Step 3: Segment Your Network Flat networks are ransomware’s best friend. Implement micro-segmentation so that even if an attacker gains a foothold in one department, lateral movement to critical systems like payroll databases or citizen record vaults is blocked.
Step 4: Deploy AI-Powered Endpoint Detection and Response (EDR) Replace legacy antivirus with behavioral EDR tools. Configure real-time alerts for ransomware-specific indicators: mass file renaming, shadow copy deletion, and encryption activity. Ensure your SOC team has clear playbooks for each alert tier.
Step 5: Establish Immutable Backup Infrastructure Follow the 3-2-1-1 rule: three copies of data, two different media types, one offsite, one offline/immutable. Test restoration quarterly. Many agencies discover their backups are corrupted or incomplete only during an actual incident.
Step 6: Run Ransomware Tabletop Exercises Simulated attacks expose gaps in your response playbook before a real attacker does. Include legal, communications, and executive leadership ransomware response is not just an IT problem. It’s a governance problem.
Step 7: Integrate Threat Intelligence Into Your Workflow Subscribe to CISA’s automated threat sharing (AIS) feed. Connect your SIEM to curated government threat intel to ensure your defenses are informed by the latest ransomware group TTPs (Tactics, Techniques, and Procedures).
Real-World Use Cases
Columbus, Ohio — Interrupted, Not Defeated In July 2024, Columbus faced a significant ransomware incident attributed to the Rhysida group. The city’s investment in network segmentation and offline backups allowed core emergency services to remain operational while remediation proceeded. Their experience reinforced that government data security requires layered resilience not just prevention.
State of Colorado — Zero Trust in Practice Colorado’s Office of Information Technology began a Zero Trust implementation in 2023, starting with identity and access management reforms. By enforcing least-privilege access across 17 agencies and deploying continuous authentication monitoring, they reduced unauthorized access attempts by over 60% within the first year.
CISA’s Ransomware Vulnerability Warning Pilot (RVWP) Launched federally in 2023, CISA’s RVWP proactively notifies government entities of known vulnerabilities actively exploited by ransomware groups before an attack occurs. This is defending your community against cyber threats at scale: proactive, data-driven, and public sector-specific.
Best Practices & Expert Tips
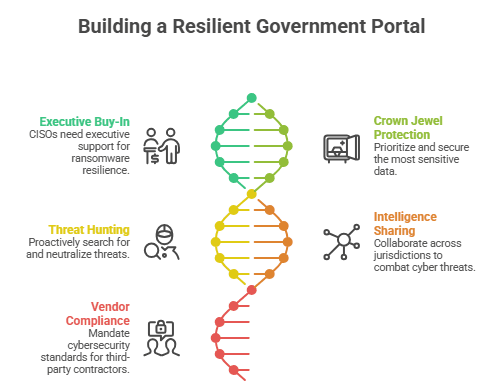
- Treat Cybersecurity as Critical Infrastructure Policy, Not IT Policy: CISOs need a seat at the budget table. Ransomware resilience requires executive buy-in, not just technical resources.
- Prioritize Crown Jewels First: Not all data is equal. Identify your most sensitive datasets voter rolls, public benefits records, law enforcement databases and harden those first with the strictest controls.
- Invest in Threat Hunting, Not Just Detection: Reactive detection catches known threats. Proactive threat hunters search for attacker behaviors that haven’t yet triggered alerts. In dwell time studies, ransomware operators often reside in government networks for 30–60 days before deploying. Hunters find them first.
- Share Intelligence Across Jurisdictions: Government cyber threats don’t respect geographic boundaries. State fusion centers and the MS-ISAC (Multi-State Information Sharing and Analysis Center) provide free threat intelligence specifically for state and local governments. Use them.
- Require Cyber Hygiene From Every Vendor: Mandate that third-party contractors meet NIST CSF 2.0 standards. Include cybersecurity breach notification requirements in every contract. Your supply chain is your security perimeter.
Common Mistakes to Avoid
Paying the Ransom Without Legal Counsel. Payment may violate OFAC sanctions if the ransomware group is designated. It guarantees nothing data is often still leaked, and attackers return.
Assuming MFA Alone Is Sufficient. MFA reduces risk dramatically, but modern adversaries use MFA fatigue attacks and SIM-swapping. Pair MFA with anomaly detection.
Neglecting Insider Threat Vectors. Many ransomware attacks are enabled intentionally or accidentally by insiders. Monitor for unusual data access patterns and enforce strict offboarding procedures.
Testing Backups Only on Paper. Documented backup procedures mean nothing if a restoration test has never been run under pressure. Schedule quarterly recovery drills with real RTO/RPO measurements.
Siloing Cybersecurity from Continuity Planning. Ransomware response is a business continuity event. IT teams that aren’t deeply integrated with the agency’s continuity of operations (COOP) plans will be improvising at the worst possible moment.
Conclusion: The Future Belongs to the Proactive
Cybersecurity solutions for government are evolving fast and the gap between agencies that embrace this evolution and those that don’t is becoming a matter of public safety. The ransomware groups targeting government portals are sophisticated, well-funded, and patient. Defending against them requires the same qualities.
Looking ahead to 2026 and beyond, three trends will define the frontier of government cybersecurity defense:
AI vs. AI Warfare. As defenders deploy AI-powered detection, ransomware operators are training adversarial AI to evade it. The arms race is accelerating. Governments must continuously retrain and update their models.
Quantum-Resistant Cryptography. NIST finalized its first post-quantum cryptographic standards in 2024. Federal agencies must begin migrating encryption infrastructure now before quantum decryption capabilities render current protections obsolete.
Unified National Cyber Posture. The Cyber Incident Reporting for Critical Infrastructure Act (CIRCIA) is pushing toward mandatory incident reporting and coordinated response. Expect a more federated, intelligence-sharing approach to national cyber defense across all levels of government.
How Government App Maisters Can Help
Government App Maisters specializes in delivering mission-critical federal government IT solutions and cybersecurity solutions for government agencies at every level. From ransomware resilience assessments and Zero Trust architecture implementation to deploying risk intelligence platforms tailored for the public sector, Government app maisters brings deep domain expertise to the agencies defending your community against cyber threats.
In an era where a ransomware attack today on government infrastructure can disrupt essential services for millions of citizens, partnering with specialists who understand both the technology and the public sector environment isn’t optional it’s essential.
The question isn’t whether your portal will be targeted. It’s whether you’ll be ready when it is.
Frequently Asked Questions
What is a ransomware attack on government systems?
A ransomware attack on government systems is a cyberattack where criminals encrypt government data and demand payment to restore access. These attacks can shut down essential public services like 911 dispatch, utilities, courts, and citizen records until the threat is resolved.
Why are government portals targeted by ransomware?
Government portals are targeted because they hold highly sensitive citizen data, often run on outdated infrastructure, and face strong political pressure to restore services quickly making them more likely to pay. Their wide attack surface and underfunded cybersecurity teams make them attractive, high-value targets.
What are the best ransomware protection strategies for government agencies?
The best ransomware protection strategies include implementing Zero Trust Architecture, deploying AI-powered endpoint detection, enforcing multi-factor authentication, maintaining immutable offline backups, and regularly running tabletop incident response exercises. Combining prevention, detection, and rapid recovery is essential.
Should government agencies pay ransomware demands?
No, government agencies should not pay ransomware demands. Payment does not guarantee data recovery, may violate OFAC sanctions, and signals to criminals that government targets will pay inviting repeat attacks. The focus should be on resilient backups and rapid recovery instead.
How does AI help in government cybersecurity defense?
AI helps by detecting abnormal behaviors like mass file encryption or unusual login patterns in real time, far faster than human analysts. AI-powered tools can automatically isolate infected endpoints and trigger response playbooks within seconds of detecting a ransomware indicator.
How long does it take a government agency to recover from a ransomware attack?
Recovery ranges from days to several months, depending on backup quality and incident response readiness. Agencies with tested immutable backups and documented recovery playbooks can restore critical services within 24–72 hours; those without may face weeks of costly disruption.
What are the biggest cyber threats facing government agencies in 2025 and 2026?
The biggest threats include AI-powered ransomware that evades traditional detection, supply chain attacks through third-party vendors, and quantum computing threatening current encryption standards. Nation-state actors are increasingly funding ransomware groups to actively destabilize public sector infrastructure.
How can local governments defend their communities against cyber threats?
Local governments can join the MS-ISAC for free threat intelligence, enforce basic cyber hygiene across departments, partner with state cybersecurity offices, and run regular staff phishing awareness training. Strong community cyber defense starts with consistent baseline security not just big-budget tools.